SAP Cloud Connector vs. VPN: Choosing the Right Security Blueprint for Hybrid Enterprise Apps
As enterprise SaaS vendors move upmarket, they face a common “wall” at the customer’s data center: the security audit. For decades, the VPN (Virtual Private Network) was the default answer for connecting external cloud apps to on-premise SAP ECC or S/4HANA systems. However, in an era of Zero Trust architecture, the VPN’s “all-or-nothing” access model has become a primary bottleneck for IT security teams and a liability for SaaS vendors.
Understanding why, and what the alternative looks like, is now a practical requirement for any SaaS vendor serious about selling into organisations running SAP on-premise.
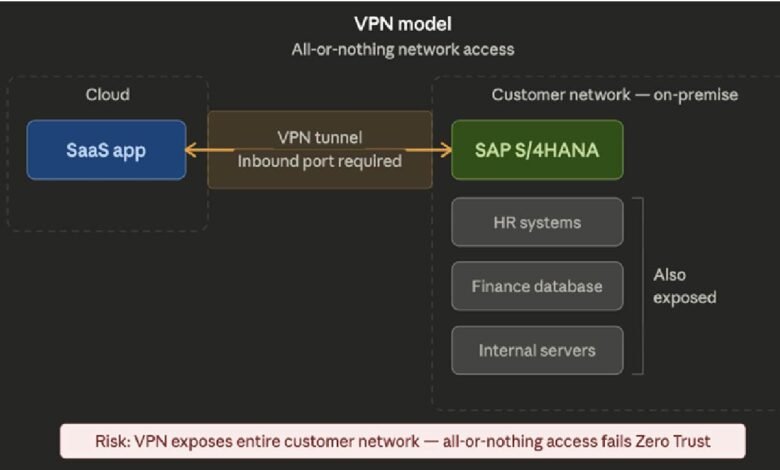
The VPN model and why it is under pressure
A Virtual Private Network creates an encrypted tunnel between two endpoints. In the context of SAP connectivity, this typically means a tunnel between the SaaS vendor’s cloud environment and the customer’s on-premise network, giving the cloud application direct access to the SAP system sitting inside that network.
The security problem with this model is the access scope. A VPN connection does not distinguish between what a connecting application needs to reach and everything else that happens to be on the same network. Once the tunnel is established, the access footprint is broad. An application connecting to SAP ECC for finance data may technically have network-level visibility far beyond what the integration requires.
This is the core tension with Zero Trust architecture, which operates on the principle that no connection should be trusted by default and every access request should be verified, scoped, and logged at the application level.
A VPN’s all-or-nothing network access model sits directly at odds with Zero Trust principles, and as enterprise security teams have adopted those principles more formally, VPN-based third-party connections have moved from routine approvals to extended scrutiny.
For SaaS vendors, this scrutiny has a commercial cost. Security reviews that once took days can now take months. Requirements to justify the access scope of a VPN connection can trigger architectural questions the product team is not prepared to answer.
In some cases, particularly in regulated industries such as financial services, pharmaceuticals, and public sector, VPN-based connectivity to SAP is now a disqualifying factor at the procurement stage.
What the SAP Cloud Connector does differently
The SAP Cloud Connector is a lightweight agent installed inside the customer’s on-premise environment. It creates an outbound-only encrypted connection to SAP Business Technology Platform in the cloud, without requiring the customer to open any inbound firewall ports.
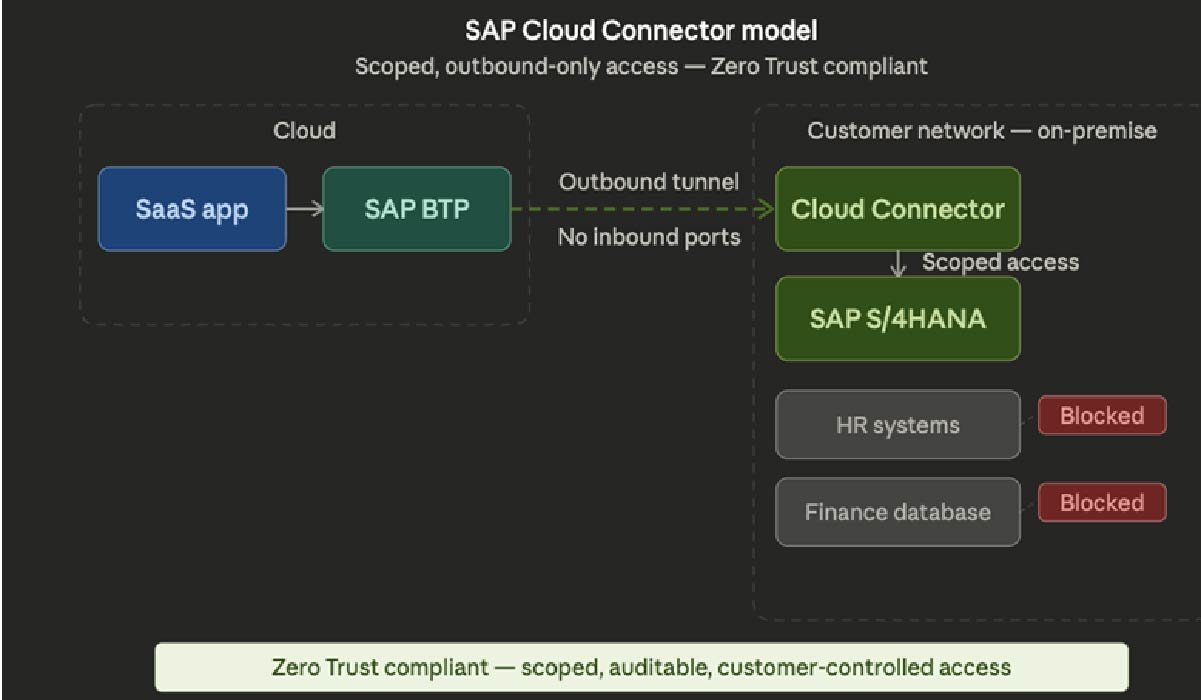
The architectural difference is significant. Rather than establishing a broad network tunnel, the Cloud Connector creates a controlled channel through which only explicitly configured resources can be accessed. The customer’s IT team defines exactly which SAP systems, which RFC connections, and which HTTP endpoints the connector exposes. Nothing outside that defined scope is reachable.
From a Zero Trust perspective, this is a fundamentally different security posture. The access is explicit, scoped, auditable, and entirely controlled by the customer. The SaaS vendor’s cloud application connects to SAP BTP, which routes requests through the Cloud Connector to the permitted on-premise resource. At no point does the cloud application have network-level access to the customer’s internal environment.
For enterprise IT security teams, this distinction matters enormously. The Cloud Connector model passes Zero Trust assessments that VPN connections do not. It produces an audit trail. It gives the customer’s team granular control without requiring them to redesign their firewall architecture or open inbound ports to an external party.
When VPN connectivity still makes sense
VPN connectivity is not obsolete in every scenario. For customers running older SAP landscapes where BTP connectivity is not yet established, or where the SAP Cloud Connector cannot be installed due to infrastructure constraints, a VPN may be the only practical option available. Some customers with highly customised on-premise environments may also have existing VPN frameworks that are more straightforward to extend than to replace.
The broader point is that VPN should be the fallback option considered when the preferred architecture is not available, not the default chosen because it is familiar. SaaS vendors who default to VPN are making their own deployment simpler at the cost of their customers’ security posture, and enterprise IT teams are increasingly aware of that trade-off.
A Quick Comparison Matrix
| Criteria | VPN | SAP Cloud Connector |
| Network access scope | Entire network | Explicitly scoped only |
| Inbound firewall ports | Required | Not required |
| Zero Trust compliance | Fails | Passes |
| Audit trail | Limited | Full and granular |
| Customer-controlled access | No | Yes |
| SAP ICC certification aligned | No | Yes |
| Security review outcome | Prolonged / blocked | Approved within existing framework |
| Deployment consistency | Custom per customer | Repeatable across customers |
| Upgrade resilience | Breaks on SAP updates | Stable — built to SAP standards |
| Regulated industry fit | Increasingly disqualifying | Approved in financial services, pharma, public sector |
Certification and the Cloud Connector
For SaaS vendors pursuing SAP certification through SAP ICC, the choice of connectivity architecture has a direct bearing on the certification process. SAP’s test scenarios for certified integrations are built around the BTP connectivity model, which includes the Cloud Connector for on-premise scenarios. An integration that relies on direct VPN connectivity rather than the Cloud Connector and BTP services is not aligned with SAP’s Clean Core standards and is unlikely to pass ICC validation without architectural changes.
This means that the connectivity decision is not just a security question. It is a go-to-market question. Vendors intending to list on the SAP Store, pursue ICC certification, or position themselves as serious participants in the SAP partner ecosystem need to build on the connectivity model that SAP supports and validates.
Getting the architecture right from the start
The Cloud Connector vs. VPN question tends to surface late in the product development cycle, usually when the first enterprise deal is in the pipeline and the security audit arrives. At that point, changing the integration architecture is expensive, disruptive, and sometimes damaging to the deal timeline.
The vendors who handle enterprise SAP connectivity well are the ones who resolved this question early, built on SAP’s published connectivity standards, and arrived at the security audit with an architecture their customers’ IT teams could approve without months of back and forth.
Working with experienced SAP cloud integration experts at the design stage, before the architecture is set, is significantly less costly than retrofitting it under commercial pressure. The SAP integration experts at AvoTechs work with SaaS vendors at exactly this stage, building connectivity architectures that hold up in enterprise security reviews and align with SAP’s certification standards from the outset.
The security audit does not have to be the wall where deals stall. With the right architecture, it becomes the stage where they accelerate.




